Imagine waking up to headlines screaming about a massive data breach, exposing thousands of customers’ credit card information to malicious hackers. The aftermath: shattered trust, financial penalties, and a tarnished reputation. As businesses increasingly rely on electronic payments, the need to protect sensitive cardholder data has never been more critical. Enter PCI compliance—the ultimate fortress safeguarding the realm of payment transactions. In this blog, we unveil the mysteries surrounding PCI compliance. Empowering you with the knowledge to protect your customers’ data and fortify your small business against the ever-looming threat of cybercrime.
What does PCI Mean?
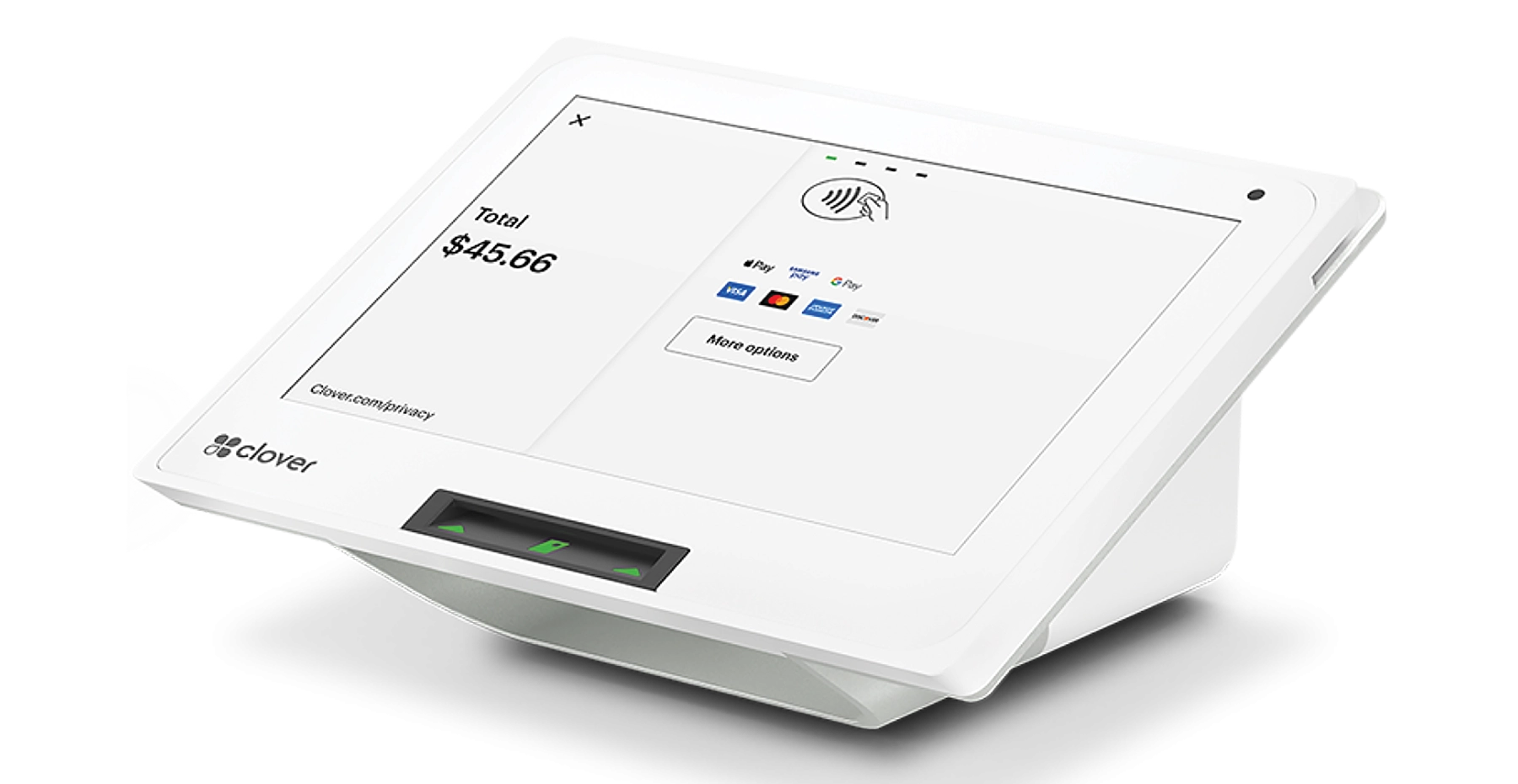
The full acronym is PCI DSS. This stands for Payment Card Industry Data Security Standard (PCI DSS). The PCI Security Standards Council (PCI SSC) is the independent organization responsible for developing, maintaining, and managing PCI DSS and other payment card security standards. PCI compliance is following a set of security standards designed to protect credit card holder data and ensure secure payment transactions. PCI compliance was established in 2006 by major card brands, including Visa, Mastercard, American Express, Discover, and JCB, and is managed by the PCI Security Standards Council (PCI SSC). PCI compliance is designed to keep cardholders and their information safe, with the main goal of reducing opportunities for attack. PCI compliance applies to any organization that accepts, processes, stores, or transmits cardholder data. The Payment Card Industry Data Security Standard (PCI DSS) sets the minimum standard for data security. PCI compliance is not legally required but is contractually enforced by major card brands and acquiring banks. Understanding PCI compliance is critical for any organization that handles credit card data.
Major credit card companies, including Visa, Mastercard, American Express, Discover and JCB, developed PCI DSS in 2004 in response to increasing data theft and fraud in the payment processing industry. They wanted to have some sort of cohesive framework for securing sensitive cardholder information, which led to the formation of the PCI Security Standards Council (PCI SSC), also known as the security standards council, to oversee and update these standards.
Before the PCI DSS was introduced, the card payment industry was experiencing weaknesses and inconsistent security protocols. There were different security measures for each brand of credit card. This means businesses had to remember which card had what security protocol and hope they were following each correctly. This made it difficult to guarantee consistent protection of sensitive cardholder data and created a lot of security holes. Credit card fraud and data breaches were prevalent because of the lack of consistency and caused businesses and consumers great financial losses.
PCI DSS Today
The need for a unified security standard became very apparent to address the growing threat of unauthorized access, breaches and misuse of cardholder data. Recognizing the need for a more robust security framework, the major credit card companies collaborated to establish the PCI DSS. The first version of the standard, PCI DSS 1.0, was released in December 2004. It provided a unified set of requirements and guidelines for organizations involved in payment card transactions.
A PCI compliance overview highlights that PCI compliance standards are designed to help merchants and service providers understand and implement security requirements to safeguard cardholder data. These standards are regularly updated by the PCI Security Standards Council to address new threats and maintain best practices.
Since its creation, there has been great technology advancements and new security threats. So, the PCI DSS has continued to evolve through updates and revisions to keep up with the current and ever changing landscape of cybersecurity. Regular updates and new versions of the PCI compliance standards are released to address emerging vulnerabilities, clarify requirements, and align with industry best practices. Version 4.0 of the PCI DSS was published on March 31st, 2022. This version is valid until March 2024.
How Businesses Can Stay Compliant
To stay PCI compliant, businesses can follow these essential steps:
A PCI compliance checklist is a practical tool that helps businesses navigate the PCI compliance process by outlining the necessary steps and best practices to achieve and maintain PCI DSS compliance. The PCI compliance process can be complex and confusing, especially for businesses working with multiple service providers. Using a checklist can help streamline the compliance process and ensure that all requirements are met. It’s important to note that PCI DSS compliance involves 12 key requirements that businesses must follow to protect cardholder data.
1. Determine Compliance Level:
PCI compliance levels categorize merchants based on their transaction volume over a 12-month period. There are four different PCI compliance levels, each determined by the number of credit card transactions your business processes annually. All merchants storing, processing, or transmitting cardholder data must be PCI-compliant, regardless of their transaction volume. Compliance requirements vary depending on the PCI compliance level, with higher levels requiring more stringent measures. Merchants with higher transaction volumes are subject to more rigorous requirements, including annual assessments by a Qualified Security Assessor (QSA). High-volume users should secure the services of a QSA who is registered to operate in the regions where they do business.
A business’s compliance level is based on the number of transactions processed annually:
-
Level 1: Over 6 million processed card transactions annually. Level 1 businesses are not eligible to use a Self-Assessment Questionnaire (SAQ) to prove PCI compliance and must undergo an annual assessment by a QSA.
-
Level 2: 1-6 million card transactions processed annually. Level 2 users have different SAQ types depending on their payment integration method.
-
Level 3: 20,000-1 million card transactions processed annually. Level 3 users also have different SAQ types based on their payment integration.
-
Level 4: Merchants that process fewer than 20,000 card transactions annually. Level 4 merchants are required to comply with PCI DSS, but validation of compliance is only required if mandated by applicable law or regulation, and they have different SAQ types depending on their payment integration method.
Other factors may also change a business’s compliance level. For example, businesses that have recently suffered a cyber attack or pose an information security risk may be elevated to a higher compliance level.
2. Understand the PCI DSS Requirements:
To achieve PCI compliance, businesses must follow specific pci requirements and pci compliance requirements as outlined in the current version of the standard. The first step in achieving PCI compliance is knowing which requirements apply to your organization. These requirements cover various areas such as network security, cardholder data protection, access control, security policies, vulnerability management, and more.
3. Conduct a Self-Assessment:
If your business qualifies for self-assessment, complete the appropriate Self-Assessment Questionnaire (SAQ) based on your compliance level. There are 9 different SAQs a merchant can choose from. How you process credit cards and handle cardholder data determines which SAQ your business needs to fill out. For example, SAQ C is for any merchant with a payment application connected to the internet, but with no electronic cardholder data storage. If you don’t have a storefront and all your products are sold online through a third party, you probably qualify for SAQ A or SAQ A-EP. The SAQ helps evaluate your security controls and identify any gaps that need to be addressed. You can find the list of all the SAQs and what merchants qualify for each, here.
4. Engage a Qualified Security Assessor:
Also known as QSA. A Qualified Security Assessor needs to conduct an on-site audit and verify your compliance if you work for a larger organization or if you need an external review. A QSA is a licensed expert who can evaluate your security procedures and offer recommendations for improvement.
5. Implement Security Controls:
Implement the essential security controls and procedures in accordance with the PCI DSS requirements and any gaps found during the self-assessment or QSA audit. Secure all system components, including network resources and computer access, by applying secure configurations and managing other security parameters such as not using vendor supplied defaults. Ensure you restrict access to sensitive data by implementing strong access control measures, including assigning unique IDs, using multi-factor authentication, and restricting physical access and physical access to areas where payment card data and stored cardholder data are handled.
Maintain a vulnerability management program by conducting regular vulnerability scans, penetration testing, and engaging an approved scanning vendor for quarterly network scans. Regularly test security systems and network security controls to identify vulnerabilities and maintain secure systems. Encrypt payment card data, including the full primary account number, during transmission over open networks, and protect stored cardholder data and sensitive authentication data by minimizing data stored and never storing sensitive authentication data post-authorization.
Document all security policies and procedures to ensure all personnel understand their responsibilities, and perform compliance validation as required by your merchant level. Use network segmentation and tokenization to reduce compliance scope and risk, and support your compliance efforts. Remember, maintaining compliance and maintain PCI compliance are ongoing processes—PCI compliance is not a one-time event but an annual process that requires continuous monitoring, regular testing, and updating of security practices.
Using a PCI-compliant processor can help reduce the burden of compliance on your business, so it’s important to avoid unreliable or insecure credit card processors that could expose you to hidden fees and added security risks. Always protect customer data and payment card data, and be aware of the risks associated with storing credit card data—store credit card data only when absolutely necessary and use secure methods. Ongoing compliance efforts are essential for maintaining compliance and reducing the risk of data breaches.
6. Train Employees:
To ensure that staff members are aware of their roles and responsibilities in ensuring PCI compliance, offer regular security awareness training. Inform them about safe cardholder data handling, avoiding phishing scams, managing passwords, and other security best practices, including how to lower credit card processing fees responsibly without compromising data security or compliance.
7. Keep Records:
Lastly, document all of your compliance activities, including policies, practices, assessments, and any corrective measures you may have taken. These documents might be necessary for continuing compliance monitoring, validation, and audits.
Secure Credit Card Data Storage
Storing credit card data securely is a cornerstone of PCI DSS compliance and a vital step in protecting your customers’ sensitive information. When businesses store cardholder data, they become responsible for safeguarding it against unauthorized access and potential data breaches. PCI DSS standards require that any stored credit card data is protected using advanced security measures to minimize the risk of exposure.
One of the most effective ways to protect cardholder data is through encryption. Encryption transforms sensitive data, such as the primary account number, into an unreadable format that can only be accessed with the correct decryption key. This ensures that even if cybercriminals gain access to your systems, the credit card data remains protected and unusable.
Another powerful tool is tokenization. Tokenization replaces sensitive card data with unique tokens that have no exploitable value outside your secure systems. This means that even if a breach occurs, the stolen information cannot be used to commit fraud or unauthorized transactions.
In addition to secure storage, it’s crucial to use secure protocols when transmitting cardholder data across networks. This prevents sensitive data from being intercepted during payment processing or other business processes.
By implementing these security measures, your business not only meets PCI DSS compliance requirements but also demonstrates a commitment to protecting cardholder data and maintaining customer trust. Remember, secure credit card data storage is not just about compliance—it’s about safeguarding your business and your customers from the costly consequences of data breaches.
Make Sure Your Business is PCI Compliant
Maintaining PCI compliance is crucial for the security, goodwill, and survival of your small business. It is also a legal necessity. Achieving PCI compliance involves several key steps, including the remediation phase—where you fix any vulnerabilities identified during the assessment—and the final phase of reporting, which requires compiling and submitting a report to your acquiring bank and the major payment card brands to verify compliance. To ensure that the fortress of PCI compliance stays impenetrable and to earn the trust of your valued customers, take the appropriate actions, train your team, and exercise continual vigilance.